Firewalling xen bridge
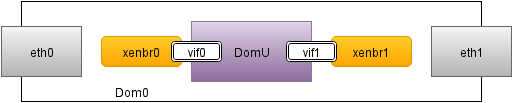
Occasionally you will wish to block certain ports to your DomUs from Dom0. By default you wish to allow any traffic from and to DomU but for some security considerations, I found it to be wise to block some ports to and from my clients DomUs. One such port range is for example IRC. Although it can be routed trough alternate ports, most of automated malicious scripts use default ones. It's quite handy to block them so they ain't able to contact home.